Available Security Measures for Internet-Connected Data Loggers
by Dana Worley | Updated: 12/07/2016 | Comments: 2
The Internet of Things offers a lot of advantages in today’s culture. There are consumer devices that let you monitor and control mood lighting and music in your home, keep track of last week’s leftover dinner in your refrigerator, and help you brew a cup of coffee while monitoring how many coffee beans you have left in the pantry. The list of Internet-connected devices that are designed to make our lives easier grows daily. However, as we have recently seen in the media, there is a downside to this widely distributed connectivity: Internet-connected devices that are not properly secured can pose a security risk.
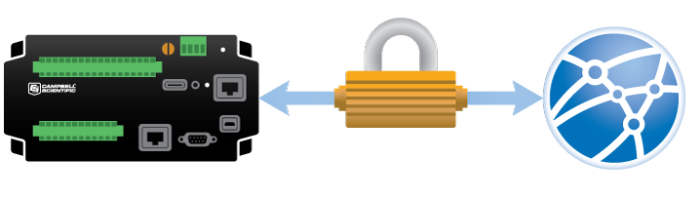
Unlike consumer device manufacturers, at Campbell Scientific, data logger security and integrity of data have always been at the top of our minds when we develop instruments. In this article, I’ve provided a summary of the security measures available for our Internet-connected data loggers. I hope you can use this information to help secure your data logger, data, and network, while ensuring that you have the access you need to accomplish your data collection tasks.
A Two-Fold Approach to Security
Campbell Scientific's data acquisition systems are represented as two parts—the data logger hardware and the software used to manage the hardware. Security measures for these two components are addressed separately in this article; however, please keep in mind that a combination of these measures ensures the overall integrity and reliability of your data acquisition system.
Securing Hardware: CR3000, CR1000, CR800/850, CR300/CR310, and CR6 Dataloggers
Follow the tips in each of the three steps below:
- Secure the network services in your data logger, which include HTTP, FTP, Telnet, and PakBus/TCP.
- Turn off all the services that you don’t need.
- Disable Ping to prevent discovery of a data logger on your network.
- If FTP is enabled, set the FTP user name and password.
- If HTTP is enabled, set the HTTP user name and password. You do this by creating and storing a .csipasswd file on the data logger.
- Set the PakBus TCP password. The PakBus TCP password controls access to PakBus communication (that is, the protocol used by LoggerNet and other software) over a TCP/IP link.
- If encrypted data transmission is important to you, set the PakBus encryption key to encrypt all PakBus packets using AES-128 encryption.
- Set the five-digit numeric password in the data logger.
- If your CRBasic program files contain sensitive information, encrypt them.
- For extra protection, hide CRBasic program files on your data logger's CPU drive.
- You can use the Device Configuration Utility (DevConfig) to disable or allow network services, and to set passwords in your data logger, as needed.
- Secure your peripherals.
- Enable security in peripheral devices, where available.
- Make sure to change the default user names and passwords in devices connected to your data logger, such as cellular modems and cameras.
- Monitor your data logger for changes.
- Track program and operating system signatures.
- Track CPU, USR, and CRD file contents.
Security Implementation in Software Using LoggerNet Admin
You can use the LoggerNet Admin software program to communicate with and program your data logger, as well as to collect data. LoggerNet Admin includes a Security Manager, which you can use to set up five levels of user accounts. Each level grants varying degrees of access to functionality in the software (and thus, control of the data logger). Look for a future blog article that covers LoggerNet Admin Security in more detail.
Conclusion
Just like any other Internet-connected device, no data acquisition system is without its vulnerabilities. The risks associated with Campbell Scientific's systems, however, can be mitigated with proper measures. The key to securing your data logger, data, and network is to put the controls in place to ensure your data logger is secure, while still allowing the access you need to complete your data acquisition tasks.
If you have questions about security related to Campbell Scientific's hardware or software, leave a comment below, or contact your local Campbell Scientific office or representative.
















 Dana Worley, now retired, joined Campbell Scientific, Inc., in 1997. As an Application Engineer, Dana provided technical support and training to customers, and she developed online and written documentation. Other roles included management of R&D projects, software products, and a Software Test and Support group. Dana most recently managed our Technical Support Team in the Client Services department. She enjoys hiking, biking, traveling, and photography, and she is an accomplished artist, specializing in kiln-formed glass.
Dana Worley, now retired, joined Campbell Scientific, Inc., in 1997. As an Application Engineer, Dana provided technical support and training to customers, and she developed online and written documentation. Other roles included management of R&D projects, software products, and a Software Test and Support group. Dana most recently managed our Technical Support Team in the Client Services department. She enjoys hiking, biking, traveling, and photography, and she is an accomplished artist, specializing in kiln-formed glass.
Comments
Vim | 12/08/2016 at 01:13 AM
This is a very interesting blog post. Another point to add, the advantages of including all the levels of security could be to reduce data throughput. If you are using cellular modems or even IP based satellite modems, costs can be expensive. If you have someone constantly sending requests (ping or just a brute force IP based attacks) to a public facing IP address for the datalogger then data costs can mount. Having these levels of security can reduce or deny some of these request/attacks.
Dana | 12/09/2016 at 09:20 AM
Hello Vim,
There are many ramifications of having an unsecure device on an accessible network, and costs are certainly a big one. Thank you for point this out. Best -- Dana
Please log in or register to comment.